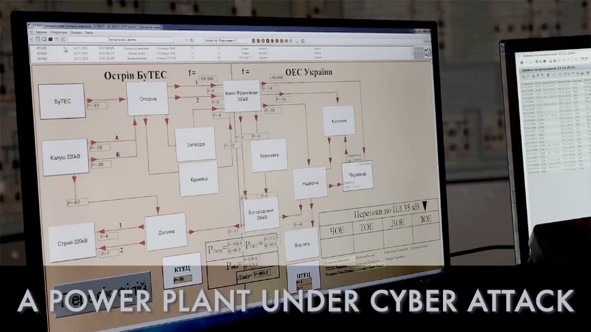
NERC “lesson learned” Report reveals details of first cyber U.S. power grid cyber attack
An anonymous Western United States utility became the first to report a malicious “cyber event” that disrupted US grid operations. In a report highlighting the “lesson learned” from a past incident, NERC (North American Electric Reliability Corporation) said hackers repeatedly rebooted firewalls causing communication outages in multiple remote generation sites in the western United States, […]
Do we need to apply Cyber Security for Distribution Networks?
Power distribution supplies critical infrastructure sectors, including water, transportation, telecommunications, health and financial sectors. With the development of smart cities, smart cars and smart homes, our dependence on electricity distribution continues to grow exponentially. To cater the growing electricity demand, power distribution utilities are adopting digital technologies and communication to increase their efficiency and competitiveness […]
EPA Security Assessment on Public Water Systems

Public Water Systems (PWS) are increasingly facing cyber threats that pose a significant risk to the safety and integrity of drinking water treatment and distribution processes, paralleling the potential impact of physical attacks. Addressing this concern, on March 3, 2023, the US Environmental Protection Agency (EPA) issued a crucial memorandum to State Drinking Water Administrators. […]
IoT Security: Safeguarding the Connected World
Navigate the complexities of securing Internet of Things (IoT) devices, addressing the risks associated with the proliferation of connected technologies and offering solutions to fortify IoT security.
The Rise of Ransomware: Understanding, Preventing, and Recovering

Examine the growing threat of ransomware, understanding its impact on individuals and businesses, and learning proactive measures for prevention and effective recovery strategies.
Social Engineering: Unraveling the Art of Human Hacking

Delve into the psychology behind social engineering attacks, uncovering the tactics used by cybercriminals to exploit human behavior and offering practical tips to fortify against such manipulative strategies.
Demystifying Encryption: A Closer Look at the Shield of Digital Privacy

Explore the intricate world of encryption and its pivotal role in securing digital information, providing insights into how this technology safeguards privacy and data integrity.